Help Desk: (651) 328-8905
Sales Inquiries: (651) 323-1775
Security Resources
Security Threats are everywhere
Email, Social Media, Websites, Viruses, Malware, Web Applications, Weak Passwords, Unsecured Networks, Ex-Employees, the list goes on.
With new threats developing every day, it can be impossible to stay ahead of the bad guys and keep your business assets protected.
RYMARK has identified 15 Ways to Protect Your Business from a CYBER ATTACK!

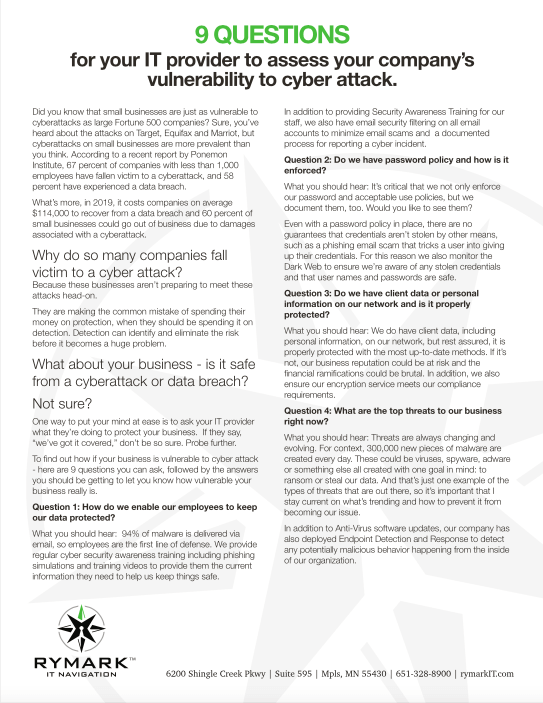
Vulnerable to Cyber Attacks?
Need to know how vulnerable your company is to cyber attacks?
Network and IT security is important to keep your business safe from hacks and breaches. These questions with your security team can help you evaluate how vulnerable your company is and where you can improve.
RYMARK has identified 15 Ways to Protect Your Business from a CYBER ATTACK!
Don’t lose productivity during your move
RYMARK IT Navigation is a local Managed Service Provider (MSP) providing proactive IT security and support to small-midsized businesses, small government, private EDU and nonprofit organizations. Join our successful team.

Small oversights can become big problems
It’s difficult enough to maintain business productivity, IT security and your bottom line on a “normal day.” Now you’re moving? If you don’t have a clear plan to move your people, your data, and your business, you could experience lost productivity, damaged client relationships, or compromised security. With proper planning, you will save money, reduce stress, maintain security and ensure a successful move. The experts at RYMARK have assisted many clients with their business moves and we’ve put together our Moving Checklist to help you plan yours.
Download it now or schedule a no cost move review. We look forward to helping you.


Working from Home?
Protect your work devices from online security threats with our guide to working safely from home.
We know that working from home is new to some people and possibly overwhelming. One of RYMARK's goal is to enable you to work as securely and productively as possible from home. By following the five simple steps outlined in our guide to working more securely from home will keep you and your family much safer from cyberattacks
Click the button to download the PDF.
