Help Desk: (651) 328-8905
Sales Inquiries: (651) 323-1775
Have You Outgrown Your Minneapolis IT Support Company?
At RYMARK IT Navigation, your team of trustworthy IT experts, we provide Minneapolis organizations with reliable, proactive IT support and cybersecurity solutions for seamless operations.



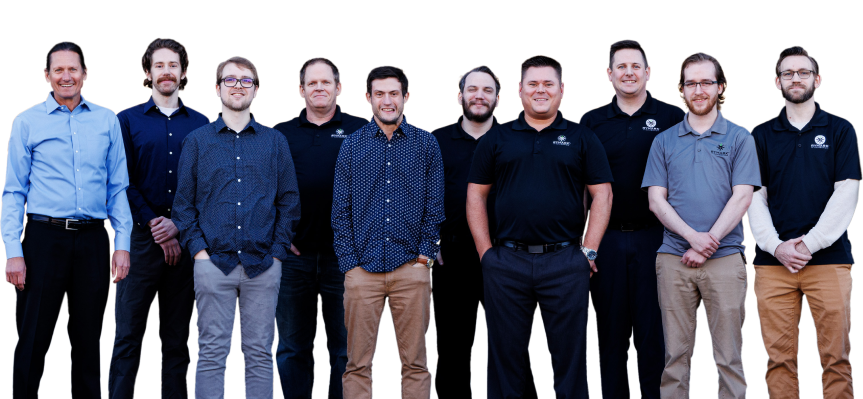
IT Support Specialists You Can Trust
Why Organizations Choose RYMARK IT Navigation
Our core values make the difference
Customer-First Approach
Our proactive, customer-focused culture prioritizes addressing your organization needs, ensuring dependable support with prompt, meaningful responses to keep operations running smoothly.
Problem Solving
As a trusted Minneapolis IT support company, we use a refined six-step process to effectively tackle any IT challenges, providing solutions that align with your organization's objectives and goals.
Best-Practice Solutions
Committed to integrity, honesty, and openness, we deliver IT solutions grounded in trust, transparency, and respect, building lasting partnerships with our clients.
Peace of Mind
As a leading IT support & IT security company, our advanced security measures protect your organization from cyber threats, allowing you to focus on success while we safeguard your digital assets.
Team Players
With a collaborative spirit, we uphold high standards and bring out the best in each other, passionately striving to exceed every goal.
CBS Minnesota Cybersecurity Tips by RYMARK
Featured on CBS Minnesota, RYMARK shares practical, expert-led cybersecurity tips to help businesses and individuals stay protected—starting with simple strategies like password management and digital hygiene.
How can you safely remember your passwords?
What happens when you select "report junk" for texts and emails?
Protect your organization from CYBER ATTACKS
Download RYMARK’s Free Security Audit Guide to See How Your Organization's Security Stacks Up.
Security Threats Are Everywhere
With new threats developing every day, it can be impossible to stay ahead of the bad guys and keep your business assets protected.
Email, social media, websites, viruses, malware, web applications, weak passwords, unsecured networks, ex-employees—the list goes on.
Without the right security measures, your assets are susceptible to theft, destruction, or ransom which can lead to lost productivity, irreparable damage to your reputation, and even put you out of organization.
Let RYMARK IT Navigation, your trusted Minneapolis IT Support & IT Security Company help you with our cybersecurity services!
The IT Support Specialists You Can Trust

Mark Sommerfeld & Ryan Chester
Managing Partners
We Help You Navigate the Rough Waters of IT Security
As business owners for more than 25 years, we understand the commitment you’ve made and the importance of protecting the organization you’ve worked so hard to build. The experts at RYMARK IT Navigation, your trusted Minneapolis IT Support & IT Security Company, are continually evaluating the latest threats and security measures to protect, detect, and respond to them. We provide solutions that both protect your organization's assets and enable your employees to work more efficiently.
Feel like you’ve been down this road before?
Let us assure you that we place our priority on client relationships, not on turning a high profit. We’re here to maximize your current IT infrastructure, not drain your bank account. We’ll likely even lower your IT costs rather than raise them.
Call (651) 323-1775 today to schedule your appointment. We’re ready to start important IT conversations with organizations just like yours.
How Can We Help?
Our Services
Managed IT
We’ll manage all of your IT services for a flat-rate fee.
Cybersecurity
Comprehensive protection against evolving digital threats to safeguard your organization.
IT Projects
Expert planning and execution of IT solutions tailored to your needs.
Network Security
Safeguarding your network effectively from unauthorized access and cyber threats.
Endpoint Patching & Critical Update Management
Ensuring devices stay secure with timely updates and patches.
Password & Multi-Factor Authentication Management
Strengthening access controls with secure authentication solutions.
Email Security
Protecting your email communications from phishing and malware attacks.
Backup & Disaster Recovery
Never worry again about losing your data in the event of any disaster.
Security Awareness Training
Educating employees to recognize and prevent cybersecurity threats.
Endpoint Protection, Detection & Response
Proactive defense against endpoint threats with real-time monitoring.
24/7/365 SOC
Continuous monitoring and swift response to threats by a dedicated security team.
Help Desk Support
Reliable, expert assistance for all your IT issues, anytime you need it.
How Vulnerable Is Your Company to Cyber Attacks?
These 9 questions can help you evaluate how vulnerable your company is and where you can improve.
Your Security and Peace of Mind Starts Here
As an IT support & IT security company, we help you stay ahead of cyber criminals, stay ahead of your competition, reduce IT distractions, and experience the peace of mind that comes with the confidence that you’re protecting your organization.
We value you and your organization. With this in mind, we have established these promises to every client.
Our Service Level Agreement
Customer Satisfaction Guarantee
Monthly/Quarterly Updates & Reports
No Hidden Costs
Clear Plan & Expectations
What Clients Say About Us
Business Technology Insights
Explore expert insights, trends, and expert advice on the ever-evolving landscape of information technology. Dive in to discover how we leverage cutting-edge solutions to empower organizations and drive innovation.

How to Protect Your Business from Shadow IT Risk
It's no secret that technology has completely transformed the way we do business. From cloud computing to mobile devices, there are countless tools and resources available to help companies operate more efficiently and effectively.
However, these benefits also come with risks, particularly when it comes to unapproved technology being used at your company. This is known as "shadow IT," and it can pose significant threats to the security and stability of a business.
In this guide, we will discuss what shadow IT is, its potential risks, and, most importantly, how to protect your business. By being proactive and taking the necessary precautions, you can prevent shadow IT from causing harm to your company.
What is Shadow IT?
Shadow IT refers to any technology or software that is used within a company without the approval or knowledge of the IT department. This can include everything from personal smartphones and laptops to cloud services and productivity apps.
Essentially, anything that is not officially sanctioned or supported by the company's IT team falls under the umbrella of shadow IT. And, with the rise of remote work and the increasing accessibility of technology, it's only becoming more prevalent in the workplace. In fact, a study by Gartner found that 41% of employees reported using unauthorized tech for work purposes.
Why Does Shadow IT Happen?
So why do employees turn to shadow IT in the first place? It's not usually out of malicious intent; instead, it's often due to:
Convenience: Employees may find unapproved tools easier or faster to use than official ones, especially if they feel the approved solutions are outdated or cumbersome.
Productivity: Some employees believe that using their preferred apps or devices will help them work more efficiently or collaborate more effectively.
Lack of Awareness: In some cases, employees don't realize the risks associated with using unauthorized technology or may not even be aware of company policies regarding approved tools.
Gaps in IT Support: When employees feel their needs aren't being met by the IT department, they may take matters into their own hands to find solutions.
The Risks of Shadow IT
While it may seem harmless on the surface, shadow IT can bring many risks and challenges to a business. These include:
Security Vulnerabilities
Using unapproved tools can expose a company's sensitive data to security breaches and cyberattacks. Shadow IT often lacks the necessary security protocols and updates, leaving systems vulnerable to hackers.
Reduced Visibility and Control
With people using different tools and devices, it becomes challenging for the IT team to track and manage all technology in use. This lack of control can make enforcing compliance with regulations or company policies difficult.
Data Silos and Loss
When employees use their own tools and devices, relevant data may not be shared with the rest of the team or backed up on company servers. This can lead to data silos, making it difficult for teams to collaborate and causing loss of important information.
Increased IT Costs
Tracking and addressing unauthorized technology retroactively can strain IT resources and increase costs. Fixing issues caused by shadow IT often takes time and effort that could have been avoided with proper oversight.
How to Protect Your Business from Shadow IT
Addressing shadow IT requires a proactive approach. Here's how you can safeguard your business while empowering employees with the tools they need:
Foster Open Communication
Create a culture where employees feel comfortable discussing their technology needs. By understanding their challenges, companies can recommend suitable tools and eliminate the need for shadow IT.
Develop Clear Policies
Establish and communicate clear guidelines on what technology and tools are approved for use. Include explanations of why these policies are essential to the company's security and compliance.
Provide User-Friendly Tools
Ensure that approved tools and systems are intuitive, efficient, and capable of meeting employee needs. Conduct regular surveys or feedback sessions to assess satisfaction with the current tech stack.
Educate Your Team
Train employees on the risks of shadow IT and the importance of using approved tools. Provide practical examples of how shadow IT can lead to security breaches or compliance issues.
Use Monitoring Software
Deploy monitoring tools to track the use of unapproved apps and devices. While this shouldn't replace trust, it can provide insights into potential risks and help you address them quickly.
Take Control of Shadow IT
Shadow IT doesn't have to be a looming threat to your business. By understanding why it happens and taking proactive measures to address it, you can mitigate risks while fostering a secure, productive work environment.
Remember, the goal isn't to stifle innovation but to strike a balance between empowering employees and maintaining control over your company's technology landscape. So, take steps today to protect your business from the hidden risks of shadow IT.
Frequently Asked Questions
What are IT security services?
IT security services encompass measures and practices to protect your systems, networks, and data from potential threats. These services include but are not limited to network security, data encryption, access controls, vulnerability assessments, penetration testing, and incident response.
What are managed IT service providers?
Managed IT service providers (MSPs) are companies that remotely manage a organization's IT infrastructure and services, such as network management, cybersecurity, and data backup, on a subscription basis. They help organizations streamline operations, reduce costs, and ensure IT systems run efficiently.
What are the benefits of cybersecurity services?
IT security services encompass measures and practices to protect your systems, networks, and data from potential threats. These services include but are not limited to network security, data encryption, access controls, vulnerability assessments, penetration testing, and incident response.
What services does RYMARK offer to organizations in Minneapolis?
We provide a range of services, including Managed IT Services, IT Projects, Cybersecurity Services, Network Monitoring and Management, Backup and Disaster Recovery Services, Vendor Management, CTO and Strategic IT Consulting, Work-from-Home Support, IT Relocation Services, and more.
How can Managed IT Services benefit my business?
Managed IT Services offer proactive management of your IT infrastructure, ensuring optimal performance, minimizing downtime, and allowing you to focus on core business activities.
What industries does RYMARK specialize in serving?
We cater to various industries, including Non-Profit Organizations, Religious Organizations, Schools and Education, Financial Service Organizations, Manufacturers, Legal Industry, Construction, and Professional and Government Services.
How does RYMARK ensure the security of our IT infrastructure?
We conduct comprehensive IT security assessments to identify vulnerabilities and implement robust security measures, including employee training, to safeguard your IT infrastructure.
What is an IT security assessment, and why is it important?
An IT security assessment evaluates your IT infrastructure to identify vulnerabilities and potential threats, providing a roadmap to enhance your organization's security posture.
How can we protect our organization from phishing attacks?
Implementing multi-factor authentication, using strong passwords, and conducting regular employee training on recognizing phishing attempts are effective strategies to protect against such attacks.
What steps can we take to improve our network security?
Regular network assessments, implementing firewalls, ensuring up-to-date antivirus software, and conducting employee training are crucial steps to enhance network security.
How does RYMARK support remote work solutions?
We offer Work-from-Home Support services, ensuring secure and efficient remote work setups for your employees.
What should we do if we experience a data breach?
Contact our IT support team immediately. We provide Backup and Disaster Recovery Services to help you respond effectively to data breaches and minimize potential damage.
How can we ensure compliance with industry regulations?
Our IT Security and Support services include assessments and employee training to help your organization comply with relevant industry regulations and standards.
At RYMARK, we believe in using our expertise to strengthen not only businesses, but also the communities they serve. That’s why we’re a proud member of Get Support, Give Support, a nationwide initiative that brings together IT providers to offer free technology services to nonprofits making a difference locally.
For every new client that signs up for our managed IT services, we donate remote monitoring agents to a nonprofit organization in our community. These tools help charities secure, manage, and optimize their IT environments, without adding to their overhead, so they can focus fully on their missions.
Whether it’s helping a shelter stay connected or enabling an education nonprofit to operate more efficiently, this initiative allows us to turn everyday business into tangible, lasting impact.
Because when nonprofits have the right tech support, they can do what they do best: change lives.
Simplify Your IT and Secure Your Business With a Trusted Managed IT Services provider
Work with a local IT Support Company that understands what it takes to keep your technology aligned with business success. With RYMARK IT Navigation by your side, you get:
Reliable, forward-thinking IT support tailored to your organization
Improved system performance and stronger cybersecurity controls
Peace of mind knowing your technology is managed by experts
Contact us today to schedule your free consultation and build a stronger, more secure IT foundation for your business.




















